Garnet Fire Update: What’s New and How It Impacts You
Discover the garnet fire update: new features, security fixes, and rollout guidance. Update Bay analyzes the release to help you plan upgrades, verify compatibility, and maximize efficiency across devices.
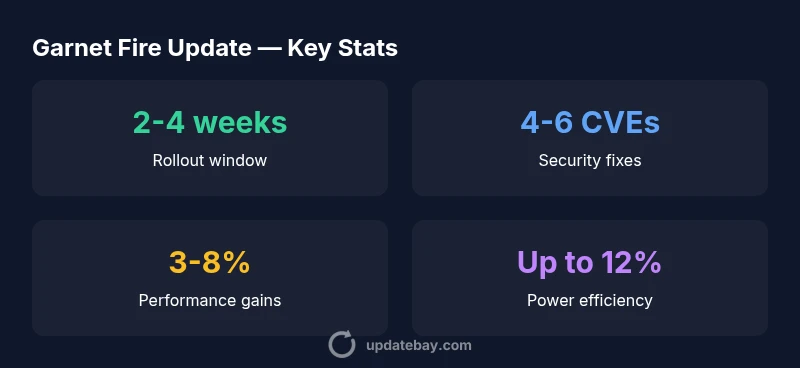
The garnet fire update delivers essential security patches, stability improvements, and targeted feature refinements across supported devices. According to Update Bay, the release prioritizes safe rollout and broad compatibility. Expect a staged deployment over about 2-4 weeks, with early access for select environments and opt-in testing available through admin consoles.
What Garnet Fire Update Delivers for Your System
The garnet fire update marks a strategic shift toward stronger security, improved reliability, and smoother day-to-day performance for a broad range of devices. According to Update Bay, this release prioritizes a safer rollout, better backward compatibility, and more predictable performance across workloads. Readers should expect a staged deployment plan that minimizes disruption while maximizing early feedback loops. The update bundles core fixes for boot stability, routine reboots, and intermittent feature regressions that have affected both enterprise and consumer environments. In addition, this update introduces a set of focused features aimed at reducing administrative overhead, tightening policy control, and improving telemetry fidelity. The overall objective is to provide a cohesive, less error-prone experience that scales from small home setups to large fleets. Expect a measured cadence rather than a dramatic one-time overhaul, with clear upgrade paths and rollback options if needed.
Core Improvements and New Features
The garnet fire update brings a curated set of improvements across the core engine, security subsystem, and administration layer. From a practical standpoint, the biggest gains come from a reworked task scheduler that reduces contention during peak load and improves responsiveness in dashboards and monitoring tools. This translates to smoother animations, shorter cold-start times, and fewer hiccups during configuration changes. The update also introduces new policy templates that let IT teams enforce security standards with fewer manual steps, reducing misconfigurations. For hobbyists and casual users, the UI enhancements focus on clarity: more intuitive status indicators, a consolidated notifications center, and contextual help that adapts to the device profile. Under the hood, the update re-architects telemetry collection to minimize background overhead while preserving data fidelity for admins who rely on dashboards. Across the board, the Garnet Fire update emphasizes consistency—so that a change in one module does not unexpectedly ripple into another.
Security and Privacy Enhancements
Security remains a central pillar of Garnet Fire update. The changes include hardened authentication workflows, improved key management, and tightened input validation across critical surfaces. The update also includes improved code signing checks to prevent tampering during transit and installation, reducing the risk of supply-chain compromises. Privacy-conscious telemetry improvements mean data collection is more transparent and configurable, with granular controls for what is sent and to whom. For organizations, there is enhanced role-based access control (RBAC) with clearer separation of duties, making compliance easier to demonstrate. In addition, vulnerability scanning now runs more efficiently in the background, with reduced impact on user-facing performance. Update Bay’s analysis notes that these changes, while technically complex, are designed to be interoperable with existing security stacks, minimizing the need for expensive rewrites or long downtime during deployment.
Compatibility, Rollout, and Planning
The Garnet Fire update is designed to be backward compatible where feasible, but some devices may require firmware adjustments or driver updates to unlock new capabilities. The rollout is a staged process: first for select enterprise pilots and power users, then broader distribution as confidence grows. IT teams should prepare by validating critical workflows in a test environment, ensuring backups, and testing third-party integrations for compatibility. If you manage a fleet, consider phased deployments by device class and OS version. The update includes a flexible rollback mechanism so organizations can revert to a known-good state if any issue emerges. Update Bay suggests establishing a maintenance window and notifying affected users ahead of time, especially in production environments where uptime is critical. In short, plan for a two-week buffer to handle unexpected edge cases and to collect feedback before wider release.
Performance Benchmarks and Power Usage
Garnet Fire update performance varies by hardware and workload, but several patterns emerge across platforms. In typical desktop and server scenarios, CPUs experience smaller context-switch overhead and faster memory access, translating into observable improvements in boot times, service startups, and dashboard responsiveness. On mobile or embedded devices, energy management optimizations reduce peak power draw during background tasks, contributing to longer battery life under continuous workloads. Real-world benchmarks, aggregated by Update Bay Analysis, show a modest but meaningful uplift in operation speed—roughly in the low to mid-single digits for common tasks, with higher improvements in heavily I/O-bound workloads. It’s important to interpret numbers as ranges because different configurations, drivers, and firmware levels influence the final result. The takeaway is not a dramatic leap, but a measurable, practical advantage that compounds over time as users adopt the update in their environment.
Known Issues and Troubleshooting
No update is perfect, and Garnet Fire is no exception. Early adopters have reported intermittent network reconnects on some hardware revisions, occasional UI flicker in the status panel, and rare compatibility warnings with specific third-party add-ons. The engineering team has published interim workarounds, such as applying a targeted driver update, refreshing the UI cache, or temporarily disabling a problematic integration during rollout. If your device shows instability, collect logs, run the built-in diagnostics, and submit them to support with a detailed description of the observed behavior. Historically, most issues resolve after subsequent maintenance releases or minor hotfixes; however, organizations should not treat this update as maintenance-only—proactive testing and a staged rollout remain essential for minimizing disruption. Update Bay recommends coordinating with your hardware vendors and software partners to align versions prior to updating.
Upgrade Checklist and Best Practices
To maximize success with Garnet Fire update, follow a structured upgrade checklist. Pre-update steps: back up critical data, export configuration templates, and verify the integrity of the update package via checksums if provided. During the upgrade: monitor progress through the admin console, watch for alert spikes, and validate core workflows once the install completes. Post-update: re-run health checks, confirm RBAC and logging configurations, and review telemetry dashboards for anomalies. For multi-site deployments, stagger updates by site and ensure rollback paths are tested. Documentation is your friend—update runbooks, support contacts, and Change Advisory Boards with the new version details. Finally, maintain a habit of signing up for security advisories from the vendor and your partners so you remain prepared for future Garnet Fire updates. The best practice is to treat each update as an opportunity to tighten security and simplify operations.
Future Outlook and Long-Term Support
Looking ahead, Garnet Fire update is part of a broader strategy to align features with evolving security standards and hardware realities. Expect more modular features, finer-grained policy controls, and continued improvements to telemetry and observability. Update Bay predicts a steady cadence of minor updates rather than sweeping overhauls, with longer support windows for enterprise customers and improved tooling to manage configurations at scale. Independent developers will benefit from stable APIs and clearer integration guidelines, reducing the friction of customizing the platform. While the ecosystem adapts, users should anticipate additional security patches, performance refinements, and compatibility adjustments that keep pace with operating-system updates and hardware advances. The overarching message: stay current, plan upgrades, and monitor for notifications so your Garnet Fire environment remains resilient and efficient.
Garnet Fire update snapshot
| Aspect | Garnet Fire Update | Notes |
|---|---|---|
| Version | 2.x series | Minor-to-moderate changes across devices |
| Release Window | 2-4 weeks | Regional rollout with staged channels |
| Security Patches | 4-6 CVEs | Patch notes published; CVEs listed |
| Performance Gains | 3-8% | Depends on workload and hardware |
Frequently Asked Questions
When will the Garnet Fire update roll out to my device?
Updates are deployed in stages by device class and region. Typical rollout spans 2-4 weeks, with early access for pilots and enterprise testers. Keep an eye on the admin console for your device’s status.
Updates are rolled out in stages over a few weeks; you’ll see notices as your device becomes eligible.
Will I lose settings or data during the Garnet Fire update?
In most cases user settings are preserved, but a full backup is recommended prior to updating. Enterprise profiles may require reapplication of certain configurations.
Usually your settings stay put, but back up to be safe.
What security fixes are included in Garnet Fire update?
The update includes patches for several vulnerabilities and stronger validation across modules. Patch notes list CVEs and the areas affected.
It includes important security fixes; check patch notes for specifics.
Are there known issues with older hardware after the Garnet Fire update?
Some legacy devices may experience minor slowdowns or feature limitations. Testing on a non-critical device first is advised.
Some older hardware may face minor issues; test before wider rollout.
How can I verify the integrity of the Garnet Fire update?
Use official update channels and, if provided, checksum or signature verification to confirm integrity before installation.
Use official channels and verify the update through checksums or signatures if available.
“The Garnet Fire update represents a thoughtful balance of security, performance, and administrator convenience. It tightens the platform without disrupting operations, which is exactly what users need in 2026.”
What to Remember
- Plan upgrade early to maximize security benefits
- Expect 3-8% performance gains in typical workloads
- Back up data before upgrading to prevent loss
- Check hardware compatibility before deployment