Update and Shutdown Bug: A Practical Side-by-Side Comparison
Explore the update and shutdown bug across major OS families. This analytical comparison explains causes, diagnosis steps, patch timelines, and practical strategies to minimize downtime while maintaining security and stability.

TL;DR: The update and shutdown bug can cause failed shutdowns during patch cycles on multiple OS families. Windows, macOS, and Linux each show unique failure modes, but the remedy centers on managed patch timing, cautious auto-restart settings, and verified backups. According to Update Bay, the most reliable mitigation combines timely security updates with tested rollbacks and explicit user restart policies. This quick verdict helps set expectations while you read the full comparison. In practice, disable auto-restart during critical windows and verify patch integrity before deployment.
What is the update and shutdown bug?
The update and shutdown bug refers to scenarios where applying OS updates, firmware patches, or driver installs triggers an improper shutdown, a reboot loop, or a system that refuses to power down cleanly. This issue can manifest during routine maintenance, security patch cycles, or feature rollouts, and it affects multiple major platforms. In practice, users may see a stuck shutdown screen, a reboot that spawns a loop, or a near-blank boot sequence after updates complete. According to Update Bay, this family of issues is more about interaction between update services, power-management policies, and device firmware than about a single faulty update. The keyword update and shutdown bug captures the recurring tension between timely patching and predictable system shutdowns, especially as devices span diverse hardware and software stacks in 2026.
Why this issue matters to users and IT teams
For everyday users, an unexpected shutdown during an update can result in lost work, corrupted files, and frustration. IT teams face scheduling dilemmas, risk management, and the challenge of coordinating firmware and driver updates across fleets. Update Bay analysis shows that the most effective mitigation is not a single patch but a coordinated approach: align maintenance windows with deployment cohorts, test patches in controlled environments, and communicate clearly with end users. The broader impact includes potential security gaps if patches are delayed, so a disciplined process is essential for resilience.
Where the bug shows up: Windows devices, macOS devices, Linux systems
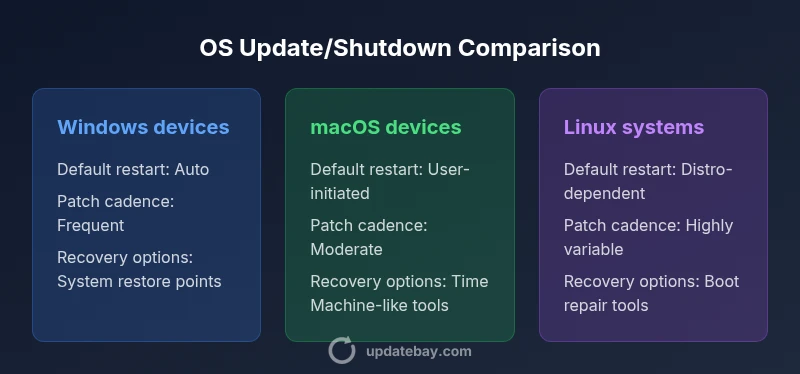
Across Windows, macOS, and Linux, the update and shutdown bug reveals platform-specific behavior during patch cycles. Windows devices may experience auto-restart loops after updates, macOS systems can fail to shut down cleanly when a software update conflicts with power management, and Linux environments often depend on distro-specific tooling and governors for update triggering. The differences matter because they shape how you implement controls, test plans, and rollback strategies. For organizations, this means tailoring maintenance playbooks to each platform while preserving a unified governance model.
Root causes: software, firmware, and hardware interactions
Root causes of update-and-shutdown failures typically involve a three-way interaction: software update services, firmware/BIOS power policies, and hardware timer states. When an update requires a firmware reboot, mismatches between the update sequencing and the firmware’s own restart logic can trigger a shutdown hang. Driver state during the final stages of a patch can also stall the shutdown process. Even simple misconfigurations—such as aggressive power-saving policies or outdated firmware—can create fragile update paths. The key is to map update steps to the device’s power-management flow and verify compatibility across software layers before deployment.
How to safely diagnose and reproduce
Begin with a controlled lab or pilot group that mirrors your production environment. Reproduce the issue by initiating a standard patch cycle in a constrained maintenance window and monitoring the shutdown sequence step by step. Collect logs from the update agent, the boot manager, and the firmware interface. Look for common indicators: stalled shutdown entries, repeated reboot loops, or delayed firmware post-update resets. Create a baseline checklist of hardware, firmware, and software versions to compare against when diagnosing.
Immediate workarounds for end users
If you encounter an update-related shutdown problem, start with non-destructive steps: pause auto-restart, ensure all work is saved, and schedule a maintenance window. Use a controlled reboot after updates complete, rather than a forced power-off. Where available, trigger a manual shutdown using the operating system’s shutdown command or menu, which often completes a cleaner power-down. Keep a device off the network during patch windows to avoid interference from concurrent processes. These steps reduce risk of data loss and salvage a stable state for further remediation.
Longer-term fixes: patches, firmware, and driver updates
Longer-term mitigation hinges on a combination of verified patches, updated firmware, and compatible drivers. Establish a test environment that mirrors production and validate updates with representative workloads. Prioritize patches with documented reliability histories and ensure rollback procedures exist for every device class. Maintain up-to-date firmware levels that align with your patch cadence, and document the exact restart behavior introduced by each update. Institutions should implement standardized rollback paths, repeatable configuration baselines, and cross-team communication to minimize downtime during future cycles.
Vendor patch timelines and reliability considerations
Patch cadence varies by platform and vendor, influencing how organizations plan maintenance. While some ecosystems push patches monthly and others quarterly, reliability often depends on pre-release testing and post-release hotfixes. Update Bay analysis shows that the most robust strategies combine a staged rollout with clear rollback policies and user-awareness campaigns. Relying on a single update without a tested contingency plan raises the risk of unexpected shutdown behavior across fleets and devices.
Practical deployment strategies for organizations
Build a governance framework that defines maintenance windows, patching scopes, and user communications. Segment devices into cohorts by risk and criticality, then apply patches in staged waves with explicit validation checks before broadening the rollout. Implement automated backups and verify restoration procedures before applying updates. Maintain a centralized incident playbook that outlines escalation paths, rollback steps, and post-mortem reviews. A disciplined approach reduces downtime and improves resilience against update-induced shutdown issues.
Quick-start checklist for affected devices
Create a minimal, actionable checklist that IT staff can follow during patch weeks: (1) verify battery/AC power stability, (2) disable auto-restart, (3) test patches in a sandbox, (4) perform controlled reboots, (5) confirm clean shutdown with logs, (6) enable user communications, (7) schedule backups, (8) document outcomes for future cycles. This checklist should be integrated into your change-management process and revisited after each patch cycle to improve reliability over time.
Feature Comparison
| Feature | Windows devices | macOS devices | Linux systems |
|---|---|---|---|
| Default restart behavior | Auto-restart after updates (version dependent) | User-initiated restarts commonly required | Distro-dependent; may require manual scheduling |
| Patch cadence | Frequent, with irregular release timing | Moderate, with scheduled updates | Highly variable across distros |
| Data risk during reboot | Moderate to high if work not saved | Low if autosave and backups enabled | Moderate to high depending on configuration |
| Recovery options post-failure | System recovery points and resets | Backup snapshots and recovery tools | Boot repair and distro-specific recovery tools |
| User controls to prevent auto-restart | Explicit restart windows and policy controls | User-initiated controls via UI | Depends on distro: update-notifier and unattended upgrades |
Positives
- Clarifies cross-platform trade-offs for timely patching
- Encourages structured maintenance windows to reduce downtime
- Supports policy alignment across devices and teams
- Improves security posture by emphasizing tested rollbacks
- Promotes proactive communication with end users
Downsides
- Patch instability can still cause reboot issues
- Diverse platform behavior complicates unified workflows
- Rushed fixes may introduce new bugs or incompatibilities
- Reliance on vendor cadence can delay critical patches
Structured maintenance with platform-specific mitigations outperforms ad-hoc patching
The Update Bay team recommends a disciplined approach: staged rollouts, tested rollbacks, and clear restart policies tailored to each OS family. This reduces downtime and improves patch reliability across devices.
Frequently Asked Questions
What is the update and shutdown bug?
The update and shutdown bug refers to failures where a system does not shut down cleanly during or after applying updates. It can cause stuck shutdown screens or reboot loops across multiple OS families. Proper diagnosis focuses on update sequencing, power policies, and firmware compatibility.
The update and shutdown bug describes a failure to shut down cleanly during updates. We diagnose it by checking update sequencing and firmware compatibility.
Which platforms are most affected?
Windows, macOS, and Linux environments all show distinct failure modes related to patch cycles. Each platform has unique restart behaviors and recovery tools, so platform-specific mitigations are essential.
Windows, macOS, and Linux all show patch-related shutdown issues, with different recovery tools needed for each.
How can I identify if my system is affected?
Look for indicators such as stalled shutdowns, unexpected restarts during patch cycles, or error logs near shutdown events. Correlate timestamps with patch deployments and firmware updates to confirm a pattern.
Watch for stuck shutdowns and restarts around update times, then check logs to confirm a pattern.
What immediate steps should I take if I encounter this bug?
Pause auto-restart, save all work, and schedule a controlled reboot within a maintenance window. Ensure backups exist and verify integrity before retrying updates.
Pause auto-restart, save work, and reboot during a maintenance window with checkpoints and backups.
Are there known fixes or patches?
Patches and firmware updates addressing shutdown interactions are released by vendors periodically. Validate fixes in a test environment and apply only after successful verification.
Vendor patches can fix these issues; test first before deploying widely.
Does this bug affect data integrity?
There is potential for data loss if a shutdown occurs during write operations. Regular backups and sudden shutdown mitigations reduce risk, but consistent patch testing remains critical.
There can be data loss risk during interrupted writes; backups help mitigate this.
What to Remember
- Plan maintenance windows with cross-platform alignment
- Disable auto-restart during critical updates
- Test patches before broad deployment
- Maintain reliable backups and rollback paths
- Communicate clearly with users about patch schedules