Update and Shutdown Never Shuts Down: A Practical 2026 Comparison
An analytical comparison of automatic updates vs scheduled maintenance windows, focusing on uptime, security, and practical guidance for 2026. Update Bay provides evidence-based recommendations.
TL;DR: A strict 'update and shutdown never shuts down' policy is impractical for most devices. The best approach combines rolling updates with a scheduled maintenance window, validated rollbacks, and monitoring. This comparison explains why hybrid strategies outperform nonstop automation in real-world environments. Read on for details, scenarios, and actionable guidance.
The promise and practical limits of update policies in 2026
The phrase update and shutdown never shuts down captures a desire for uninterrupted operation, but it’s not a realistic baseline for most devices. According to Update Bay, modern systems balance continuous protection with occasional, carefully managed maintenance. Real-world deployments rely on rolling updates, staged rollouts, and robust rollback plans to minimize downtime while preserving security. In this section we explore why a hard no-downtime promise is typically replaced by adaptable policies that protect data integrity and service levels without throwing away control. We’ll examine the drivers of update strategy—from device constraints to organizational risk tolerance—and set the stage for a data-backed comparison later in this article.
Core Concepts: Automatic Updates vs Maintenance Windows
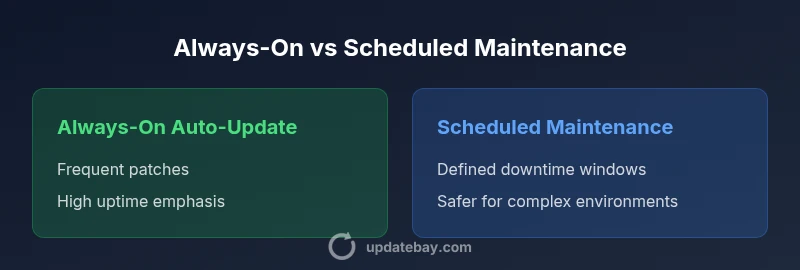
At the heart of any update strategy are two competing philosophies: automatic, always-on patching and scheduled, maintenance-window deployments. Automatic updates maximize patch speed and reduce administrative burden but can surprise users with reboots or brief downtime. Maintenance windows, conversely, centralize upgrade time, offer predictability, and enable thorough testing, but can delay critical fixes. A practical policy often blends the two: critical security patches are prioritized and deployed automatically with safe rollback, while feature updates occur within defined windows. Across devices—from consumer smartphones to enterprise servers—the aim is to maintain trust and uptime while ensuring compliance with security requirements. The keyword update and shutdown never shuts down often arises in discussions about resilience, but the most effective policies recognize trade-offs and provide clear, auditable guidelines rather than absolute guarantees.
Key Differences: Security, Uptime, and update and shutdown never shuts down
This section highlights how different policies perform on core criteria: security posture, uptime guarantees, user control, and operational overhead. Auto-update models excel at rapid patching and reducing idle risk, but can cause unplanned reboots. Scheduled maintenance emphasizes predictable outages, deeper testing, and safer rollouts but may delay urgent fixes. The real-world takeaway is a spectrum, not a binary choice. Organizations tailor policies to their risk appetite, asset criticality, and regulatory landscape, while keeping a clear trail of decisions and rollback options.
Real-world Scenarios: Consumer Devices vs Enterprise IT
Home devices often benefit from stronger defaults toward auto-patching with optional maintenance windows for feature updates, whereas enterprise IT departments require rigorous change control, auditing, and phased deployments. In practice, most mixed environments deploy critical security patches automatically, with quarterly feature updates scheduled during low-usage periods. This hybrid approach reduces exposure to exploits while preserving productivity. Update Bay’s guidance emphasizes testing, user communication, and rollback readiness for both consumer and enterprise contexts.
Implementation Tactics: Rolling updates, Canary Deployments, and Blue-Green Strategies
A practical path is to implement rolling updates that gradually propagate changes across a fleet, combined with canary deployments to catch issues early. Blue-green deployments provide a safe cutover path by maintaining parallel environments and switching traffic when confidence is high. Each tactic reduces risk and provides clear rollback options. Documented procedures, predefined exit criteria, and automatic rollback mechanisms help keep the system resilient while still delivering timely patches. The modern approach blends automation with human oversight to prevent ‘update-induced outages.’
Performance and Resource Considerations: Bandwidth, CPU, and energy impact
Updates consume network bandwidth, processor cycles, and sometimes storage space. A rolling, staggered approach minimizes peak load and avoids saturating networks during business hours. In devices with limited power budgets, updates should be scheduled for off-peak times or powered-by-constant sources. Energy efficiency and resource planning become part of the update policy, especially for large-scale deployments. Monitoring tools should track patch download progress, installation times, and reboot durations to optimize future windows.
Risk, Failure Modes, and Preparedness: Planning for failed updates
No update strategy is risk-free. Failure modes include incompatible drivers, partial rollouts, and unexpected reboots. Preparedness involves robust rollback procedures, automated monitoring, and clear escalation paths. Regular drills for rollback and rollback verification help ensure that when things go wrong, teams can recover quickly without substantial downtime. Emphasize test environments that mirror production to catch issues before they affect users.
Governance, Compliance, and Audit Trails: Keeping authorities happy
Governance requires transparent change control, documented risk assessments, and auditable patch histories. Compliance frameworks often demand evidence of timely patching and documented rollback capabilities. Use centralized dashboards to present patch status, maintenance windows, and incident responses. This not only satisfies auditors but also builds stakeholder trust in the update strategy.
Hybrid Strategies: Policy Templates and Example Configs
Develop policy templates that combine automatic critical patching with scheduled feature updates. Example config: automatic patching for critical CVEs with a 24–72 hour rollback window, and a quarterly feature-update window scheduled during low-usage periods. Include canary stages and monitoring dashboards. Templates help scale governance across teams and devices while preserving uptime and security.
Practical Guidelines for 2026: Step-by-step plan for organizations of all sizes
- Define risk tiers for assets and classify patches by urgency. 2) Establish a default policy for automatic critical patches and a separate window for features. 3) Implement canary testing with metrics like failure rate and rollback success. 4) Deploy blue-green or rolling updates to minimize service disruption. 5) Maintain audit trails and run regular disaster recovery drills. 6) Review and adjust maintenance windows based on feedback and performance data. 7) Communicate policies clearly to users and stakeholders. This structured approach aligns with Update Bay recommendations and emphasizes practical, measurable outcomes.
Authoritative Sources and Reading List
- Authoritative guidance: https://www.nist.gov
- Public safety and patch guidance: https://www.cisa.gov
- Incident response and patch management: https://us-cert.cisa.gov
Comparison
| Feature | Always-On Auto-Update | Scheduled Maintenance Window |
|---|---|---|
| Update Frequency | Continuous / real-time | Periodic (weekly/monthly) |
| Downtime Required | Minimal background restarts | Defined but brief downtime during window |
| User Interaction | Minimal; largely automatic | Requires user confirmation at start of window |
| Security Coverage | Broad, rapid patches | Urgent patches may wait for window |
| Resource Impact | Higher at patch events | Spread over scheduled times |
| Best For | Environments prioritizing speed and uptime | Environments needing predictable outages and testing |
| Rollback Capacity | Automatic rollback options frequently available | Defined rollback steps within window |
Positives
- Minimizes downtime with automatic patching
- Enhances security posture with timely updates
- Reduces administrative overhead and manual work
- Faster deployment of critical fixes across devices
- Scales well for large fleets with centralized control
Downsides
- Potential for unexpected reboots during active use
- Risk of update failures impacting uptime if not properly managed
- Can introduce compatibility issues during rapid patches
- Delays in feature updates due to testing in windows
Hybrid approach with policy-driven maintenance windows and rolling updates
A balanced policy that automates critical patches while scheduling feature updates minimizes downtime and security risk. Canary testing and robust rollback are essential. Update Bay’s assessment favors a configurable hybrid model over extremes.
Frequently Asked Questions
What does 'update and shutdown never shuts down' actually mean in practice?
It’s a guiding principle, not a literal guarantee. Real systems use hybrid policies to minimize downtime, prioritizing critical patches while scheduling windows for larger updates. The goal is resilience, not zero downtime.
It’s a guideline for resilience, not a promise of zero downtime. Teams mix automation with planned windows and rollback plans to keep systems secure and available.
Is auto-updating safe for all devices?
Auto-updating is safer for many devices, especially when patches are critical. However, it can cause unexpected reboots or compatibility issues. Pair auto-patching with testing, canaries, and rollback capabilities.
Auto-update helps patch critical issues quickly, but pair it with testing and canaries to avoid surprises.
How can I minimize downtime during updates?
Use rolling updates, staggered deployments, canary testing, and blue-green cutovers. Schedule feature updates in off-peak windows and keep emergency patches automatic with rollback.
Roll out updates in small steps, test first, and keep a quick rollback plan ready.
What is a canary deployment and when should I use it?
A canary deployment releases changes to a small subset before full rollout. It helps catch issues early without affecting all users. Use it for high-risk patches or major feature updates.
Canaries test changes on a tiny group before a full rollout, catching issues early.
How do I roll back an update if something goes wrong?
Maintain automated rollback scripts and snapshots. Validate rollback in a staging environment, then trigger a controlled switch to the previous state with clear escalation paths.
Keep rollback scripts ready and test them before you need them.
Do these strategies differ for mobile devices vs desktops?
Mobile ecosystems often rely on stronger controlled update channels with user opt-in and less dramatic reboots. Desktop and server environments benefit from centralized policies and audit trails. Tailor policies to the platform's update lifecycle.
Mobile tends to be more controlled; desktops and servers need stronger centralized governance.
What to Remember
- Assess asset criticality to tailor patch urgency
- Adopt rolling updates with canary testing for safety
- Schedule maintenance windows to control downtime
- Implement robust rollback mechanisms and audit trails
- Monitor patch performance and adjust windows over time